WLAN protocols and devices are the building blocks that make wireless local area networks (WLANs) function. Here’s a breakdown of the key elements:
WLAN Protocols:
These protocols define the communication standards and procedures for devices operating in a WLAN. Here are some prominent examples:
- IEEE 802.11 Standards: This is a family of standards developed by the Institute of Electrical and Electronics Engineers (IEEE) that define the physical (PHY) and logical (MAC) layer functionalities for WLANs. Common versions include:
- 802.11a: Operates in the 5 GHz band, offering higher speeds but shorter range compared to 2.4 GHz.
- 802.11b: Operates in the 2.4 GHz band, providing wider range but lower speeds due to congestion.
- 802.11g: Combines the features of 802.11a and 802.11b, offering both 2.4 GHz and 5 GHz options with improved speeds.
- 802.11n (Wi-Fi 4): Introduced MIMO (Multiple-Input, Multiple-Output) technology for increased data rates.
- 802.11ac (Wi-Fi 5): Offers wider channels and higher modulation schemes for faster speeds compared to 802.11n.
- 802.11ax (Wi-Fi 6): Latest standard, featuring improved efficiency, capacity, and performance enhancements like MU-MIMO (Multi-User MIMO) for better multi-device handling.
- Security Protocols: WLAN security protocols ensure secure communication within the network. Common options include:
- WEP (Wired Equivalent Privacy): An outdated and insecure protocol, no longer recommended due to vulnerabilities.
- WPA (Wi-Fi Protected Access): Provides improved security compared to WEP, with WPA2 being the most widely used version.
- WPA3 (Wi-Fi Protected Access 3): The latest and most robust security protocol, offering enhanced encryption and connection protection.
WLAN Devices:
These are the physical components that make up a WLAN and enable communication between devices. Some of the frequently used devices are listed below:
- Wireless Access Point (AP): Acts as a central hub for the WLAN, connecting wireless devices to the wired network and managing communication within the network.
- Wireless Client Devices: These are laptops, smartphones, tablets, printers, smart TVs, and other devices equipped with Wi-Fi adapters that can connect to the network and access resources.
- Wireless Repeaters/Extenders: These devices can extend the range of an existing Wi-Fi network by amplifying the signal, but they can introduce drawbacks like reduced bandwidth.
- Wireless Routers: Often combine the functionalities of an access point and a wired router, providing internet access and managing both wired and wireless connections within a network.
Understanding these protocols and devices is crucial for:
- Setting up and configuring your WLAN: Choosing the appropriate standards and security protocols for your needs.
- Troubleshooting network issues: Identifying potential problems related to incompatible protocols or device configurations.
- Optimizing network performance: Selecting the right devices and configuring them for optimal coverage, speed, and security.
By understanding these WLAN protocols and devices, you can create a reliable and secure wireless network that meets your specific needs and provides a seamless connection experience for your devices.
In the context of WLANs (Wireless Local Area Networks), a Station (STA) refers to a wireless client device that can associate with an access point (AP) and participate in network communication. Here’s a breakdown of what STAs are and their role in a WLAN:
What is a Station (STA)?
An STA is any device equipped with a Wi-Fi adapter that can connect to a WLAN. These devices can be:
- Laptops
- Smartphones
- Tablets
- Smart TVs
- Gaming consoles
- Printers
- And other Wi-Fi enabled devices
STA Responsibilities:
- Scanning for Networks: STAs can actively search for available Wi-Fi networks (access points) within their range.
- Authentication and Association: They can initiate the authentication and association process with a chosen access point to gain access to the network.
- Communication: Once connected, STAs can communicate with other devices on the network (both wired and wireless) and access network resources like the internet.
- Power Management: STAs can negotiate power saving modes with the access point to conserve battery life.
- Data Transmission and Reception: They transmit and receive data packets over the wireless connection.
Types of STAs:
There are two main categories of STAs:
- Wireless Client: This is the most common type of STA, referring to devices like laptops, smartphones, and tablets that connect to a WLAN for internet access and resource sharing.
- Wireless Repeater/Extender: These devices act as STAs but also have additional functionalities to extend the range of an existing Wi-Fi network. They connect to the main access point and then re-transmit the signal, expanding the coverage area.
Understanding STAs is important for:
- Troubleshooting network issues: Identifying problems related to specific STAs or their connection to the network.
- Managing network access: Controlling which devices (STAs) can connect to your WLAN and implementing security measures.
- Optimizing network performance: Understanding how many STAs are connected and their resource usage can help optimize network performance.
A Basic Service Set (BSS) in infrastructure mode, also commonly referred to as an infrastructure BSS (IBSS), is the most common type of Wi-Fi network deployment. Here’s a breakdown of its key characteristics:
Components:
- Access Point (AP): Acts as the central hub of the network. It’s a dedicated device that manages communication between wireless client devices and provides a connection to the wired network (usually the internet).
- Wireless Client Devices (STAs): These are laptops, smartphones, tablets, printers, and other devices equipped with Wi-Fi adapters that connect to the AP to access the network.
How it Works:
- Client Association: Wireless client devices scan for available Wi-Fi networks (SSIDs) broadcasted by APs within their range.
- Authentication and Association: A chosen AP is selected, and the client device initiates an authentication process with the AP to verify its identity and network access rights. Upon successful authentication, the device associates with the AP and becomes part of the BSS.
- Communication: Once associated, client devices can communicate with each other within the BSS and access network resources like the internet through the AP. The AP forwards data packets between wired and wireless devices.
Benefits of BSS (Infrastructure Mode):
- Centralized Management: The AP simplifies network management by providing a single point of control for configuration, security settings, and monitoring.
- Scalability: An infrastructure BSS can support a larger number of client devices compared to an Independent BSS (ad-hoc network) due to the centralized management capabilities of the AP.
- Improved Security: Security features implemented on the AP, like WPA2 or WPA3 encryption, provide a more robust security posture compared to ad-hoc networks.
- Roaming: Clients can seamlessly roam between different APs within the same network (if configured correctly), maintaining a constant connection while moving around the coverage area.
Limitations:
- Single Point of Failure: If the AP malfunctions, all client devices in the BSS lose network connectivity.
- Reliance on Wired Infrastructure: An infrastructure BSS requires a wired network connection for the AP to function and provide internet access.
Deployment Scenarios:
BSS (infrastructure mode) is the ideal solution for various network environments, including:
- Homes: Provides internet access and network connectivity for personal devices in a home environment.
- Small Offices: Offers a scalable and manageable network solution for small businesses.
- Public Wi-Fi Zones: Creates public Wi-Fi hotspots in airports, cafes, or convention centers for internet access.
- Enterprise Networks: Large organizations can utilize multiple BSSes with centralized management for secure and reliable wireless connectivity for employees and devices.
BSS (infrastructure mode) forms the backbone of most modern Wi-Fi networks. It offers a reliable, scalable, and secure solution for connecting wireless devices to a wired network and the internet, making it the preferred choice for various deployment scenarios.
SSID and BSSID
Both SSID and BSSID are crucial elements for identifying and connecting to Wi-Fi networks, but they serve different purposes:
- SSID (Service Set Identifier):
- Think of it as the network name. It’s a human-readable identifier that wireless devices can detect when searching for available Wi-Fi networks.
- Broadcast by Access Points (APs): An AP transmits its SSID so that nearby devices can find it.
- Multiple devices can share the same SSID: In some situations, multiple access points within the same network might broadcast the same SSID to create a seamless roaming experience for users moving around the coverage area.
- BSSID (Basic Service Set Identifier):
- Unique identifier for an Access Point: Unlike the SSID, the BSSID is a unique 48-bit MAC address that identifies a particular access point within a network.
- Not typically displayed: BSSIDs are not usually displayed for users to see directly. However, they can be accessed through network configuration menus on devices or using network scanning tools.
- Used for device association: Wireless client devices use the BSSID to identify the specific access point they want to connect to, especially when multiple APs share the same SSID.
Here’s an analogy to illustrate the difference:
- Imagine an apartment building. The building address (e.g., 123 Main St.) is like the SSID – a general identifier for the location.
- Within the building, each apartment has a unique door number (e.g., Apt. 502). This is similar to the BSSID, which uniquely identifies a specific access point.
Remember:
- SSID: The public name of the Wi-Fi network that you see when searching for available connections.
- BSSID: The unique identifier for a specific access point within a network, used by devices to connect to the correct AP.
ESS
An Extended Service Set (ESS) is a type of Wi-Fi network architecture that expands upon the capabilities of a Basic Service Set (BSS). Here’s a breakdown of what an ESS is and how it offers advantages over a BSS:
Concept: An ESS essentially combines multiple BSSes (each consisting of an access point and its associated client devices) into a single, logical network. These BSSes are interconnected through a wired backbone (like switches or routers), allowing for wider coverage and increased capacity compared to a standalone BSS.
Components:
- Multiple Access Points (APs): These are distributed throughout the coverage area to provide wireless connectivity.
- Distribution System (Wired Network): Connects the APs together, enabling communication and data exchange between them.
- Wireless Client Devices (STAs): These are laptops, smartphones, tablets, and other Wi-Fi enabled devices that connect to any of the APs within the ESS.
Benefits of ESS:
- Wider Coverage: By utilizing multiple APs, an ESS can provide a significantly larger wireless network footprint compared to a single AP in a BSS. This is ideal for covering large areas like offices, campuses, or public Wi-Fi zones.
- Increased Capacity: An ESS can support a higher number of connected devices compared to a BSS. The distributed architecture allows for better load balancing between APs, preventing congestion and maintaining good performance for all connected users.
- Centralized Management: ESS networks often enable centralized management through a network controller or software. This simplifies configuration, security enforcement, and monitoring of the entire network from a single point.
- Seamless Roaming: Clients within an ESS can seamlessly roam between different APs without losing connectivity as they move around the coverage area. The network appears as a single entity to the devices, ensuring uninterrupted user experience.
When to Use an ESS:
An ESS is the preferred choice for situations where a single BSS falls short:
- Large Spaces: For offices, schools, campuses, or buildings with a large footprint, an ESS ensures wider Wi-Fi coverage.
- High Device Density: Environments with a large number of users and devices, like conference centers or public Wi-Fi hotspots, benefit from the increased capacity of an ESS.
- Centralized Control: Organizations requiring centralized management and control over their Wi-Fi network infrastructure are well-suited for an ESS deployment.
Limitations:
- Complexity: Setting up and managing an ESS can be more complex compared to a BSS due to the additional hardware and configuration requirements.
- Cost: Deploying multiple APs and a wired backbone infrastructure can involve a higher initial investment compared to a single BSS.
However, an ESS offers a scalable and robust Wi-Fi network solution for situations where a single BSS is insufficient. By combining multiple access points and centralized management, ESS networks provide wider coverage, increased capacity, seamless roaming, and better control for administrators.
IBSS or Ad-hoc Network
IBSS, which can stand for Independent Basic Service Set or Infrastructure BSS (though the latter is less common), refers to a type of Wi-Fi network architecture distinct from the more widely used BSS (Basic Service Set) with an access point and ESS (Extended Service Set) with multiple access points. Here’s a breakdown of IBSS:
Concept: An IBSS, also known as an ad-hoc network, is a peer-to-peer Wi-Fi network formed directly between wireless client devices (STAs) without the need for a central access point (AP). Devices participating in the IBSS communicate directly with each other.
Components:
- Wireless Client Devices (STAs): Laptops, smartphones, tablets, or other Wi-Fi enabled devices can create and participate in an IBSS.
- No Central AP: There’s no dedicated access point involved in managing the network.
How it Works:
- Network Creation: A device initiates the creation of an IBSS by broadcasting a beacon signal with a chosen SSID (network name) and configuration parameters.
- Device Association: Other Wi-Fi devices within range can search for available networks and choose to join the IBSS based on the broadcasted SSID.
- Direct Communication: Once connected, devices can communicate directly with each other within the IBSS for file sharing, gaming, or other purposes.
Benefits of IBSS:
- Simple Setup: Creating an IBSS requires minimal configuration, making it a quick and easy way to establish a temporary network connection between devices.
- No Infrastructure Needed: No need for a dedicated access point or wired network infrastructure, making it suitable for situations where such resources are unavailable.
Limitations of IBSS:
- Limited Scalability: IBSS networks typically support a smaller number of devices compared to BSS or ESS due to limitations in managing communication between multiple peers.
- Security Concerns: Security in an IBSS can be weaker compared to networks with a central AP that enforces security settings. Proper configuration and strong encryption practices are crucial.
- Limited Range: The range of an IBSS is generally shorter compared to a network with an access point due to the reliance on device transmit power.
- No Centralized Management: Troubleshooting and managing an IBSS can be more challenging due to the absence of a central control point.
Use Cases for IBSS:
- Temporary File Sharing: Quickly share files between a small group of devices in close proximity without needing an existing network.
- Gaming on the Go: Create a temporary network for local multiplayer gaming sessions between compatible devices.
- Emergency Connectivity: Establish a basic connection between devices in situations where no other network is available.
IBSS offers a simple and convenient way to create a temporary, peer-to-peer Wi-Fi network without an access point. However, its limitations in scalability, security, and range make it less suitable for larger deployments or situations requiring robust network features.
DS (Distribution System)
In the context of wireless networking, a Distribution System (DS) refers to the wired infrastructure that connects multiple Access Points (APs) within an Extended Service Set (ESS). It acts as the backbone of the network, enabling communication and data exchange between the APs and ultimately, the wireless client devices (STAs) connected to them.
A breakdown of the key aspects of a Distribution System:
Components:
- Switches: These are network devices that act as central hubs, receiving data packets from one AP and forwarding them to the appropriate destination AP or wired network segment based on the MAC addresses.
- Routers: In some ESS deployments, routers might be used to connect the DS to the wider internet or other networks. Routers perform additional functions like network traffic management and security enforcement.
- Cabling: Ethernet cables (usually Cat5e or Cat6) connect the switches and routers within the DS, forming a wired infrastructure for data transmission.
Functions of a DS:
- Inter-AP Communication: The DS facilitates communication between different APs within the ESS. This allows devices connected to any AP to seamlessly roam and access resources on the network, regardless of which AP they are currently associated with.
- Data Forwarding: Data packets exchanged between wireless clients and the wired network (including internet access) are routed through the DS. Switches and routers within the DS ensure efficient data flow between the appropriate parties.
- Centralized Management: Some DS implementations might be integrated with a network management system, allowing for centralized configuration, monitoring, and troubleshooting of the entire ESS network.
Benefits of a DS:
- Scalability: An ESS with a DS can support a larger number of APs and connected devices compared to a Basic Service Set (BSS) with a single access point.
- Seamless Roaming: Devices can roam between different APs within the ESS without losing connectivity, providing a smooth user experience.
- Centralized Control: The DS facilitates centralized management of the network, simplifying configuration and maintenance.
Alternatives to DS:
- Wireless Distribution System (WDS): In certain scenarios, a specialized mode on some access points called Wireless Distribution System (WDS) can be used to connect APs wirelessly. However, WDS can introduce performance limitations compared to a wired DS due to potential interference and reduced bandwidth.
Choosing the Right Solution:
The choice between a wired DS and a WDS depends on several factors:
- Network Size and Coverage: For larger networks with extensive coverage areas, a wired DS is the preferred option due to its superior performance and scalability.
- Infrastructure Availability: If pre-existing wired infrastructure is available, a wired DS is a more cost-effective and reliable solution.
- Deployment Challenges: In situations where running cables might be difficult or impractical, WDS can offer a temporary or alternative solution, but with performance trade-offs.
In short, a Distribution System forms the backbone of a robust and scalable ESS network. By providing a reliable wired connection between access points, a DS enables efficient communication, seamless roaming, and centralized management for a larger Wi-Fi network deployment.
Distribution System Media (DSM)
Within the Distribution System (DS) of an Extended Service Set (ESS) network, the Distribution System Media (DSM) refers to the physical medium used to transmit data between Access Points (APs) and other network devices. It’s the “how” of data transfer within the wired backbone of the network.
Understanding DSM:
While the DS defines the logical network structure and functionalities, the DSM specifies the actual physical means of carrying data signals. Here are some common DSM options:
- Ethernet Cables: The most widely used and reliable option. Standard Ethernet cables (typically Cat5e or Cat6) provide a secure and high-bandwidth connection for data transmission within the DS.
- Fiber Optic Cables: For larger networks or situations requiring extremely high bandwidth and low latency, fiber optic cables can be used as the DSM. They offer superior data transmission capabilities compared to traditional Ethernet cables.
- Coaxial Cable: Less common in modern deployments, coaxial cable was once used as a DSM option. However, it typically offers lower bandwidth and higher susceptibility to interference compared to Ethernet or fiber.
Choosing the Right DSM:
The selection of the best DSM for your ESS network depends on several factors:
- Network Performance Requirements: For high-performance networks with a large number of devices and high data traffic, fiber optic cables might be the ideal choice. Standard Ethernet cables offer a good balance of performance and cost for most applications.
- Distance: Fiber optic cables can transmit data over longer distances without signal degradation, making them suitable for large campuses or geographically dispersed networks.
- Deployment Considerations: Ease of installation and maintenance should be factored in. Running Ethernet cables might be simpler in some scenarios, while existing fiber optic infrastructure might be leveraged in others.
- Cost: Fiber optic cables tend to be more expensive than Ethernet cables. Consider the cost-benefit trade-off based on your specific needs.
Additional Considerations:
- Network Security: Ensure the chosen DSM can support secure data transmission within the DS. Modern Ethernet and fiber optic cables typically offer built-in security features.
- Scalability: The chosen DSM should be able to accommodate future network expansion if needed.
The Distribution System Media (DSM) is a crucial element for efficient data transfer within the wired backbone of an ESS network. Understanding the different DSM options and their characteristics helps you select the most suitable solution for your specific network requirements, ensuring reliable and high-performance Wi-Fi connectivity.
Define terminology related to the 802.11 MAC and PHY
1. MSDU
2. MPDU
3. PSDU
4. PPDU
These terms represent different packet units as data travels through the various layers of the 802.11 Wi-Fi protocol stack, specifically focusing on the Medium Access Control (MAC) and Physical (PHY) layers. Here’s a breakdown of each term:
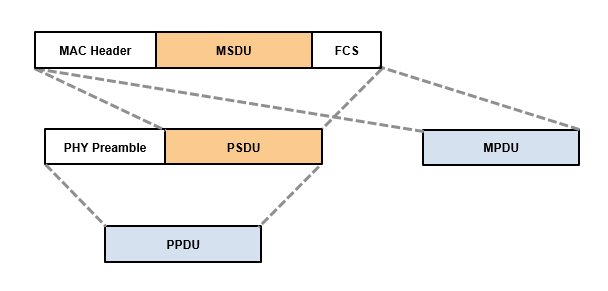
MSDU (MAC Service Data Unit):
- Layer: MAC layer
- Description: The MSDU is the largest data unit handled by the MAC layer. It represents the original data coming from a higher layer protocol (like TCP/IP) that the MAC layer needs to encapsulate and prepare for transmission over the wireless medium.
- Analogy: Think of the MSDU as a large package containing the actual data you want to send (like a document or video).
- MPDU (MAC Protocol Data Unit):
- Layer: MAC layer
- Description: The MAC layer adds headers containing information about the sender, receiver, and other control data to the MSDU. This creates the MPDU. The MPDU is the unit the MAC layer uses for communication with its peer MAC layer on the receiving device.
- Analogy: The MPDU is like the package (MSDU) with an address label (header) attached, specifying where it’s going.
- PSDU (Physical Service Data Unit):
- Layer: PHY layer
- Description: The MPDU received from the MAC layer is further processed by the PHY layer. The PHY layer might add additional headers or perform operations like fragmentation (splitting the MPDU into smaller chunks) to prepare it for transmission over the physical wireless channel. The resulting unit is called the PSDU.
- Analogy: The PSDU is like the package with the address label (MPDU) being prepared for shipment. The PHY layer might add additional packaging (headers) or break down the package into smaller parcels (fragmentation) for easier transport.
- PPDU (Physical Protocol Data Unit):
- Layer: PHY layer
- Description: The final stage involves adding the physical layer header containing synchronization signals, error correction codes, and other PHY-specific information to the PSDU. This creates the PPDU, the actual unit transmitted over the air as radio signals.
- Analogy: The PPDU is the package ready for physical delivery. It has the address label (MPDU), any additional packaging (PSDU), and a final outer layer with information for reliable wireless transmission.
The following table summarizes the above:
| Term | Layer | Description | Analogy |
|---|---|---|---|
| MSDU | MAC | Original data from higher layer | Package containing the data to send |
| MPDU | MAC | MSDU with MAC headers (addressing, control) | Package with an address label |
| PSDU | PHY | MPDU with PHY headers (optional) | Package prepared for shipment (might involve splitting) |
| PPDU | PHY | PSDU with PHY layer header (synchronization, error correction) | Package ready for physical delivery (radio signals) |
By understanding these terms, you gain a clearer picture of how data is encapsulated and processed as it travels through the different layers of the Wi-Fi protocol stack for transmission and reception.
A-MSDU and A-MPDU
A-MSDU (Aggregate MAC Service Data Unit) and A-MPDU (Aggregate MAC Protocol Data Unit) are techniques used in 802.11n Wi-Fi (Wi-Fi 4) and later standards to improve efficiency by transmitting multiple data units in a single frame. Each of the concepts and how they differ are explained below.
A-MSDU (Aggregate MAC Service Data Unit):
- Concept: A-MSDU allows combining multiple MSDUs (data units from the MAC layer) from the same source and destination into a single MPDU. This reduces overhead associated with multiple MAC headers.
- Benefits:
- Improves efficiency by reducing header overhead.
- Useful for applications that generate short data packets, like transmitting multiple small packets during web browsing.
- Limitations:
- Requires both sender and receiver to support A-MSDU capability.
- Not suitable for large data transfers, as the entire A-MSDU needs to be retransmitted if there’s an error in any of the contained MSDUs.
A-MPDU (Aggregate MAC Protocol Data Unit):
- Concept: A-MPDU takes a different approach. It combines multiple MPDUs (already containing MAC headers) into a single frame for transmission. This reduces the overhead of multiple PHY headers (physical layer headers).
- Benefits:
- Offers wider compatibility as it only requires A-MPDU support, not A-MSDU.
- More flexible, as individual MPDUs within the A-MPDU can be acknowledged or retransmitted independently in case of errors.
- Generally more efficient than A-MSDU for most traffic types.
- Limitations:
- Requires more processing power on both sender and receiver compared to A-MSDU.
Analogy:
Imagine sending multiple letters to the same recipient.
- A-MSDU: You combine multiple letters into a single envelope (MPDU) to save on individual envelopes (MAC headers). However, if there’s an issue with the envelope, all the letters inside need to be resent.
- A-MPDU: You place each letter in its own envelope (MPDU) but put them all in a larger delivery bag (A-MPDU) to reduce the number of trips. If there’s an issue with one letter, only that specific envelope needs to be redelivered.
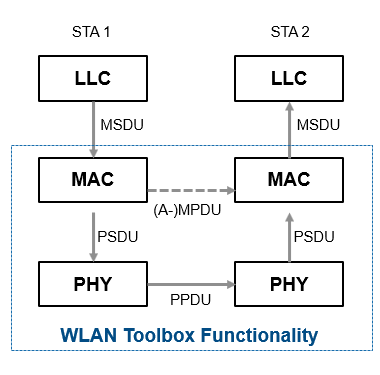
The following diagram provides a top level view of where different protocol units fall. The logical link control (LLC) data communication protocol layer is the upper sublayer of the data link layer (layer 2) of the seven-layer OSI model.
Key Differences:
| Feature | A-MSDU | A-MPDU |
|---|---|---|
| Combines | Multiple MSDUs | Multiple MPDUs |
| Reduces Overhead | MAC headers | PHY headers |
| Requires Compatibility | Both sender & receiver | Primarily receiver |
| Error Handling | Entire A-MSDU retransmitted | Individual MPDUs retried |
| Suitability | Short data packets | Most traffic types |
| Efficiency | Less efficient than A-MPDU for most cases | Generally more efficient |
A-MPDU is the more widely used and efficient technique for data aggregation in Wi-Fi networks. While A-MSDU can offer some benefits in specific situations, A-MPDU provides greater flexibility, compatibility, and error handling capabilities.
PHY Preamble and Header
In the context of 802.11 Wi-Fi communication, the PHY preamble and header are crucial elements located at the beginning of a transmitted Wi-Fi frame. They work together to prepare the receiving device for the data to follow and provide essential information for decoding the frame. The same is explained below in detail:
PHY Preamble:
- Function: The PHY preamble acts like a synchronization signal at the start of the frame. It serves two main purposes:
- Symbol Synchronization: The preamble helps the receiver synchronize its clock with the transmitter’s clock to ensure accurate decoding of the data bits. Imagine it like setting the tempo for a song before the music starts.
- Channel Estimation: The preamble allows the receiver to estimate channel characteristics like signal strength and noise levels. This information is crucial for adjusting signal processing techniques and optimizing reception in potentially noisy environments.
- Structure: The exact structure of the PHY preamble depends on the specific Wi-Fi standard (802.11a/b/g/n/ac/ax) being used. However, it typically consists of a sequence of known bits repeated multiple times. By analyzing this repetitive pattern, the receiver can lock onto the incoming signal and establish symbol timing.
PHY Header:
- Function: Once the receiver is synchronized with the transmitter’s signal thanks to the preamble, the PHY header provides essential information about the frame itself. This information allows the receiver to interpret the following data correctly.
- Content: The PHY header typically includes fields for:
- Frame Length: Indicates the total length of the entire frame, including the header and data.
- Frame Control: Specifies details about the frame type (data, control, management), receiver and transmitter addresses, and other control flags.
- Signal Rate: Informs the receiver about the data rate used for transmission, allowing it to adjust accordingly.
- Importance: The PHY header acts like a roadmap for the receiver, providing critical details about the frame’s content and configuration.
Combined Effect:
The PHY preamble and header work together seamlessly. The preamble prepares the receiver for data reception, and the header provides the necessary information to understand the incoming data. This coordinated approach ensures efficient and reliable wireless communication.
Additional Points:
- Different Wi-Fi standards might have variations in the specific preamble and header formats to accommodate different data rates and functionalities.
- Some Wi-Fi devices might support multiple preamble options depending on compatibility requirements and network conditions.
MAC Addressing
MAC (Media Access Control) addressing is a fundamental concept in Wi-Fi networking. It assigns a unique identifier (address) to every network interface card (NIC) or Wi-Fi adapter in a device. This address plays a crucial role in enabling communication between devices on a network. Here’s a breakdown of MAC addresses:
Concept:
- A MAC address is a globally unique 48-bit (6 bytes) alphanumeric code burned into the hardware of a network interface card (NIC) during manufacturing.
- The first part of the address typically identifies the manufacturer (OUI – Organizationally Unique Identifier), while the remaining portion is a unique identifier assigned by the manufacturer.
Functions:
- Device Identification: The unique MAC address allows for clear identification of individual devices on a network. This is essential for routing data packets to the correct recipient.
- Network Access Control: Some networks might use MAC filtering, a security measure that restricts access only to devices with authorized MAC addresses.
- Media Access Control: Although not its primary function in modern Wi-Fi, MAC addresses play a role in certain protocols for regulating access to the shared wireless medium.
Examples of MAC Addresses:
A typical MAC address format is XX:XX:XX:XX:XX:XX, where X represents a hexadecimal digit (0-9, A-F). Here are some examples:
- 00:11:22:33:44:55
- AA:BB:CC:DD:EE:FF
Obtaining a Device’s MAC Address:
The method for finding a device’s MAC address varies depending on the operating system and device type. Here are some general guidelines:
- Windows: Go to Control Panel -> Network and Sharing Center -> Click on your network connection -> Details. Look for “Physical Address” under “Wireless LAN adapter Wifi” or similar.
- macOS: System Preferences -> Network -> Select your Wi-Fi network -> Advanced -> Wi-Fi Address.
- Android: Settings -> About phone or About tablet -> Status -> Look for “Wi-Fi MAC address”.
- iOS: Settings -> General -> About -> Look for “Wi-Fi Address”.
Important Considerations:
- MAC addresses are permanent identifiers for a particular network interface card.
- While MAC addresses can be used for basic security measures like MAC filtering, they are not a foolproof security mechanism. More robust security protocols like WPA2 or WPA3 encryption are crucial for protecting your network.
- Spoofing (imitating another device’s MAC address) is technically possible, but security measures in most networks can help mitigate this risk.
MAC addressing forms the foundation for device identification and communication within a Wi-Fi network. Understanding MAC addresses and their role is essential for troubleshooting network connectivity issues, managing network access control, and appreciating the overall functionality of Wi-Fi technology.
MAC frame format
The MAC (Medium Access Control) frame format in 802.11 Wi-Fi defines the structure of data packets exchanged between wireless devices. It specifies the order and purpose of various fields within the frame, ensuring proper communication and data exchange. Here’s a breakdown of the typical MAC frame format:
Structure:
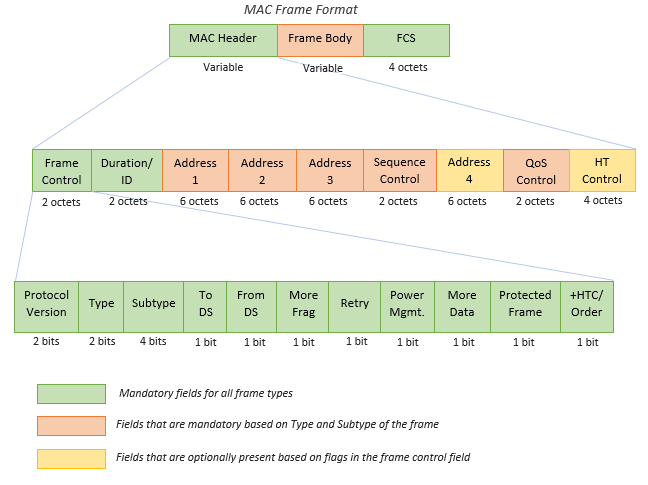
A basic MAC frame consists of three mandatory fields and a variable-length payload:
- Frame Control (FC) Field (2 Bytes):
- Version: Identifies the protocol version (usually 0 for current use).
- Type: Specifies the frame type (Data, Management, Control).
- Subtype: Further categorizes the frame type within its category (e.g., Beacon frame within Management type).
- To DS/From DS: Indicates if the frame is going to/from a Distribution System (in an infrastructure network).
- More Flag Fields: Additional control flags for specific functionalities (e.g., fragmentation, retry).
- Duration/ID Field (2 Bytes):
- Duration: In data frames, this field estimates the time required to transmit the entire frame. In control frames, it might contain an identifier.
- Address Fields (6 – 14 Bytes):
- Address fields typically include:
- Receiver Address (RA): The MAC address of the intended recipient.
- Transmitter Address (TA): The MAC address of the sending device.
- Address 1 (optional): Used in some frame types for additional addressing information.
- Address 2 (optional): Used in some frame types for additional addressing information (e.g., broadcast address).
- Address fields typically include:
- Payload (Variable Length):
- This field carries the actual data being transmitted, depending on the frame type.
- For data frames, it contains the MSDU (MAC Service Data Unit) received from the higher layer.
- The payload length can vary depending on the frame type and network conditions.
- Frame Check Sequence (FCS) Field (4 Bytes):
- A cyclic redundancy check (CRC) code calculated over the entire frame (excluding the FCS itself).
- Used for error detection at the receiving device. The receiver calculates its own FCS and compares it with the received FCS. Any discrepancy indicates data corruption during transmission.
Understanding the Importance:
The MAC frame format is fundamental for structured and error-free communication in Wi-Fi networks. By defining the organization of data within a frame, it allows devices to exchange information efficiently and reliably. The various fields within the frame provide essential details for routing, error checking, and overall network coordination.
MAC Frame Types in Detail:
The 802.11 Wi-Fi protocol utilizes three main frame types to handle different communication needs within a wireless network. Each frame type has a specific purpose and structure to ensure efficient data exchange and network management. Here’s a breakdown of these essential frame types:
- Management Frames:
- Purpose: Management frames are primarily responsible for establishing, maintaining, and terminating wireless network connections. They are like control messages that coordinate overall network operations.
- Common Functions:
- Network initialization (association, authentication)
- Beaconing (advertising the presence of an access point)
- Reassociation (switching access points)
- Deauthentication (disconnecting from a network)
- Power management (coordinating sleep modes for devices)
- Structure: Management frames typically have a variable-length payload that can carry additional information specific to the frame’s function (e.g., authentication credentials, power management settings).
- Example: A device sending a Beacon frame to announce the presence of a new Wi-Fi network.
- Control Frames:
- Purpose: Control frames are used to regulate access to the shared wireless medium and ensure efficient data exchange between devices. They act like traffic signals in a Wi-Fi network.
- Common Functions:
- Request to Send (RTS): A device requesting permission to transmit data.
- Clear to Send (CTS): An access point granting permission to transmit after receiving an RTS.
- Power Management (coordinating sleep modes for data transmission)
- Acknowledgments (ACKs): Confirming successful reception of a data frame.
- Structure: Control frames have a shorter payload compared to management or data frames, as they primarily focus on regulating data flow.
- Example: A device sending an RTS frame before transmitting data to avoid collisions with other devices.
- Data Frames:
- Purpose: Data frames are the workhorses of Wi-Fi communication. They carry the actual data traffic exchanged between devices on the network, like web pages, emails, video streams, or file transfers.
- Structure: Data frames encapsulate the MAC Service Data Unit (MSDU) received from a higher layer protocol (TCP/IP) within the MAC frame format. The MSDU is the actual user data being transmitted.
- Example: A laptop sending a data frame containing a downloaded file to a printer on the same network.
Key Differences and Working Together:
- Management frames establish and manage the network connection, while control frames regulate data flow, and data frames carry the actual user data.
- These frame types work together seamlessly. Management frames set up the network, control frames manage how data is transmitted, and data frames carry the information being exchanged.
By understanding the distinct purposes of these frame types, you gain a clearer picture of how Wi-Fi networks function and coordinate data communication between devices.
Process used to locate and connect to a WLAN – Scanning (active and passive)
When your Wi-Fi enabled device (smartphone, laptop, etc.) wants to connect to a WLAN (Wireless Local Area Network), it goes through a two-step process: scanning and association. Scanning, which can be either active or passive, helps your device discover available networks in its vicinity, while association establishes a connection with a chosen network.
Scanning – Finding Available Networks:
There are two main approaches to scanning for WLANs:
- Passive Scanning:
- Concept: In passive scanning, your device listens for beacon frames broadcasted by nearby access points (APs). Beacon frames are like advertisements sent out by APs containing information about the network, such as the SSID (network name), security settings (open, WPA2, etc.), and supported channels.
- Benefits:
- Saves battery life as the device isn’t actively transmitting anything.
- Useful in situations where active transmissions might be restricted.
- Limitations:
- Might miss hidden networks that don’t broadcast beacons.
- Relies on the APs to transmit beacons regularly, which may not always be the case.
- Active Scanning:
- Concept: In active scanning, your device transmits probe request frames directly. These frames contain information about the type of network the device is searching for (based on SSID or other criteria). Nearby APs that match the criteria respond with probe response frames containing detailed network information.
- Benefits:
- Can discover hidden networks that don’t broadcast beacons.
- More proactive approach for finding specific networks.
- Limitations:
- Uses more battery power due to active transmission.
- Might increase network congestion if multiple devices are actively scanning.
Choosing the Scan Method:
Most Wi-Fi devices use a combination of active and passive scanning. They typically start with passive scanning to conserve battery life and then switch to active scanning if no suitable networks are found passively or if the user is looking for a specific SSID.
Association – Connecting to a Network:
Once your device has identified a suitable network through scanning, it initiates the association process. This involves sending authentication frames to the chosen AP, providing any necessary credentials (like a password for a secure network), and negotiating the connection parameters. Upon successful authentication and negotiation, your device becomes a connected client on the WLAN, allowing it to exchange data with other devices on the network or access the internet (if the network provides internet connectivity).
Note that, some networks might have additional security measures beyond just password protection. These might involve additional authentication steps during the association process. Also, specific details of scanning and association procedures can vary slightly depending on the Wi-Fi standard (802.11a/b/g/n/ac/ax) being used. However, the core concepts remain the same across different standards.In summary, scanning (both active and passive) is the initial step your device takes to discover available WLANs in its range. By listening for beacons or transmitting probe requests, your device gathers information about nearby networks. Once a suitable network is identified, the association process establishes a connection, allowing your device to become a participating member of the WLAN.
802.11 Authentication
In 802.11 Wi-Fi networks, authentication is a crucial security mechanism that verifies the legitimacy of devices attempting to connect to a network. It acts as a gatekeeper, ensuring only authorized devices gain access and preventing unauthorized users or devices from joining the network. Here’s a breakdown of the 802.11 authentication process:
The Need for Authentication:
Without authentication, any device within the Wi-Fi network’s range could potentially connect, posing security risks like unauthorized access to data, network resource misuse, or even denial-of-service attacks. Authentication helps mitigate these risks by establishing trust between the device and the network.
The Players Involved:
- Station (STA): The Wi-Fi device (laptop, smartphone, etc.) trying to connect to the network.
- Access Point (AP): The wireless router or base station that provides access to the network.
- Authentication Server (optional): In some network configurations, a separate authentication server might be used to handle the authentication process.
Common 802.11 Authentication Methods:
There are several authentication methods defined in the 802.11 standard, each with varying levels of security:
- Open System Authentication (Open Auth):
- Concept: This is the most basic method and offers minimal security. The STA simply sends an authentication request to the AP, and the AP always responds with an acknowledgment, granting access.
- Security: Not recommended for use in most cases due to its lack of security. Anyone can connect to the network.
- Shared Key Authentication (WEP):
- Concept: This method uses a pre-shared key (WEP key) known to both the STA and the AP. The STA scrambles a challenge message from the AP with the shared key and sends it back. If the AP can decrypt the message with the same key, it grants access.
- Security: WEP is considered a weak encryption standard and is no longer considered secure due to vulnerabilities that can be exploited to gain unauthorized access.
- 802.1X Port-Based Network Access Control (PNAC):
- Concept: This method leverages the 802.1X protocol and often uses a separate authentication server. The STA communicates with the AP, which acts as a gateway to the authentication server. The server verifies the STA’s credentials (like username and password) using protocols like EAP (Extensible Authentication Protocol). If successful, the server grants access through the AP.
- Security: A more secure option compared to Open Auth or WEP. The use of a separate authentication server and robust protocols like EAP enhances security.
- Pre-shared Key (PSK) with WPA or WPA2:
- Concept: This is a widely used and secure method. It utilizes a pre-shared key (PSK) like a Wi-Fi password known to both the STA and the AP. WPA or WPA2 (security protocols) are used to encrypt the communication during authentication and data transmission.
- Security: WPA and WPA2 offer strong security mechanisms, making them the preferred choices for most personal and business Wi-Fi networks.
The Authentication Process:
The exact details of the authentication process can vary depending on the chosen method. However, here’s a general outline:
- The STA sends an authentication request frame to the AP.
- The AP responds with a challenge message specific to the chosen authentication method.
- The STA processes the challenge based on the method (e.g., scrambling it with a shared key or using EAP with an authentication server).
- The STA sends the response back to the AP.
- The AP verifies the response using the same method.
- If successful, the AP grants access to the STA. If unsuccessful, the STA is denied access.
Also note that..
- Some networks might combine authentication with authorization methods (like MAC filtering) to provide additional security layers.
- New Wi-Fi standards like WPA3 are being implemented to further enhance security by addressing vulnerabilities in older protocols.
By implementing robust authentication methods like WPA2 with PSK, network administrators can ensure only authorized devices gain access, protecting the network from unauthorized intrusion and potential security threats.
Open System Authentication:
802.11 Open System Authentication, often abbreviated as Open Auth, is a legacy authentication method defined in the 802.11 Wi-Fi standard. It offers the simplest way for a wireless device (STA) to associate with an access point (AP) but provides minimal security.
Here’s a breakdown of Open System Authentication:
Concept:
- Open Auth functions like a handshake with no challenge. The STA sends an authentication request frame to the AP, and the AP always responds with a positive acknowledgment, granting access to the network.
- There’s no verification of the STA’s identity or any encryption involved.
Analogy:
Imagine an open door to a building. Anyone can walk through the door and enter without needing a key or identification.
Security Considerations:
- Due to its lack of security, Open System Authentication is not recommended for most Wi-Fi networks.
- Any device within the AP’s range can connect to the network, posing security risks:
- Unauthorized access: Anyone can potentially access the network and its resources.
- Data sniffing: Unencrypted network traffic can be intercepted by unauthorized users.
- Denial-of-service (DoS) attacks: Malicious devices can connect and flood the network with traffic, disrupting legitimate users.
Use Cases (Limited):
While generally discouraged, Open Auth might be used in very specific scenarios with limited security needs, such as:
- Temporary guest networks where security is not a major concern. (Even in such cases, a WPA2 Guest network with a separate password is a more secure alternative.)
- Setting up a Wi-Fi network for testing purposes in a controlled environment.
Alternatives for Secure Connections:
For secure Wi-Fi connections, stronger authentication methods are recommended:
- Pre-shared Key (PSK) with WPA2: This is the current standard, requiring a pre-shared key (like a Wi-Fi password) for authentication and utilizing WPA2 encryption for secure data transmission.
- 802.1X with EAP: This method leverages a separate authentication server for more robust verification using protocols like EAP (Extensible Authentication Protocol).
Open System Authentication offers a simple but insecure way for devices to connect to a Wi-Fi network. Due to the significant security risks, it’s advisable to avoid using Open Auth in most practical scenarios. Opt for WPA2 with PSK or 802.1X with EAP for secure and reliable Wi-Fi connections.
802.11 Association
In the context of 802.11 Wi-Fi networks, association is a crucial step that establishes a connection between a wireless device (STA) and a specific access point (AP). It’s like a handshake that grants the STA permission to join the network and exchange data. Here’s a breakdown of the 801.11 association process:
The Need for Association:
Imagine a coffee shop with a public Wi-Fi network. While multiple devices might detect the network name (SSID) through scanning, association is required for each individual device to connect and access the internet or network resources.
The Players Involved:
- Station (STA): The Wi-Fi device (laptop, smartphone, etc.) trying to connect to the network.
- Access Point (AP): The wireless router or base station that provides access to the network.
The Association Process:
The association process typically involves the following steps:
- Authentication (Optional): In some cases, authentication might occur before association. This involves verifying the STA’s identity using methods like WPA2 with PSK (pre-shared key) or 802.1X with EAP (Extensible Authentication Protocol).
- Association Request: The STA sends an association request frame to the chosen AP. This frame contains information about the STA’s capabilities (supported data rates, security protocols) and the specific AP it wants to associate with (identified by its MAC address).
- Association Response: The AP processes the request. If successful (considering factors like authentication, available resources, and any network policies), the AP sends an association response frame back to the STA. This response confirms successful association and provides the STA with essential information for network access:
- Association ID: A unique identifier assigned to the STA for the duration of the association.
- Supported data rates: The data rates mutually supported by the STA and the AP for communication.
- Beacon interval: The frequency at which the AP transmits beacon frames to announce its presence.
- Other network parameters (optional)
- Association Confirmation: The STA acknowledges the association response frame, finalizing the connection establishment.
Successful Association:
Once the association process is complete, the STA becomes an authorized member of the network. It can now exchange data frames with the AP, allowing it to:
- Access the internet (if the network provides internet connectivity)
- Communicate with other devices on the same network (depending on network permissions)
- Utilize network resources like printers or file servers (subject to access control)
Additional Points:
- An STA can only be actively associated with one AP at a time.
- The association process can be initiated by either the STA or the AP depending on specific network configurations.
- Re-association might occur if the STA loses connection to the current AP and wants to connect to a different one or the same AP after a temporary disconnect.
- Disassociation can be initiated by either the STA or the AP to terminate the connection.
Note that Association is a fundamental process in 802.11 Wi-Fi networks. It allows devices to establish a secure connection with an AP, enabling them to participate in network communication and access resources. Understanding the association process is essential for troubleshooting connectivity issues and appreciating the overall functionality of Wi-Fi technology.
BSS Association
In the context of 802.11 Wi-Fi networks, BSS selection refers to the process a wireless device (STA) goes through to choose an access point (AP) to associate with. With potentially multiple APs broadcasting their presence in a given area, the STA needs a mechanism to decide which one to connect to for optimal performance. Here’s a breakdown of BSS selection factors:
Factors Influencing BSS Selection:
Several factors can influence an STA’s BSS selection decision:
- Signal Strength (RSSI): The Received Signal Strength Indicator (RSSI) measures the signal strength of an AP’s signal received by the STA. Generally, STAs prefer to connect to APs with stronger signals for better connection quality and data transfer rates.
- Signal Quality: Signal quality goes beyond just raw signal strength. Factors like noise levels and interference can impact the overall quality of the connection. An AP with a weaker signal but cleaner reception might be preferable to one with a strong but noisy signal.
- Security: The STA might prioritize APs offering more robust security protocols like WPA2 over those with weaker security like WEP or Open Auth.
- Supported Data Rates: The STA considers the data rates supported by both itself and the AP. Ideally, they should be compatible for optimal communication speed.
- Network Load: If an AP is already heavily loaded with connected devices, the STA might favor an AP with a lighter load for better performance. (This information might not always be readily available to the STA.)
- Configuration Settings: Some network administrators might configure specific preferences for BSS selection on managed devices, influencing which APs they prioritize.
Common BSS Selection Methods:
There are two main approaches to BSS selection:
- Load Balancing: This method focuses on distributing the load among available APs to avoid overloading any single one. It aims to achieve a balance between signal strength and network congestion.
- Highest Basic Service Set (BSS) Identifier (BSSID) Priority: In this simpler approach, the STA prioritizes APs with a higher numerical BSSID value. While not the most sophisticated method, it can be effective in situations with similarly configured APs.
The Role of Wi-Fi Standards:
Modern Wi-Fi standards like 802.11k and 802.11v can play a role in BSS selection by providing additional information to STAs. These standards allow for:
- Radio Resource Measurement (RRM): Enables STAs to gather information about nearby APs, including channel utilization and signal quality.
- Fast BSS Transition (FTM): Facilitates smoother handoff between APs when an STA roams within a network, minimizing connection disruptions.
Making the Choice:
The STA’s BSS selection process considers various factors to choose the AP that offers the best combination of signal strength, quality, security, data rates, and network load. The goal is to establish a reliable and efficient connection for data communication.
Additional Considerations:
- User preferences might influence BSS selection in some cases. For instance, a user might manually select a preferred AP even if another one has a slightly stronger signal.
- BSS selection is an ongoing process. An STA might re-evaluate its connection and potentially switch to a different AP if conditions change (e.g., signal strength weakens, another AP becomes available).
Note that BSS selection is a crucial mechanism in Wi-Fi networks, ensuring STAs connect to the most suitable AP for optimal performance. By considering various factors and leveraging features of modern Wi-Fi standards, BSS selection helps maintain a seamless and efficient wireless network experience.
Connecting to Hidden BSS
Connecting to a hidden SSID (network name) on a Wi-Fi network requires a little more effort compared to joining a visible network. Here’s what you need to know:
Understanding Hidden SSIDs:
- A hidden SSID is simply a Wi-Fi network that doesn’t broadcast its name (SSID) openly. This can be done for various reasons, such as:
- To deter unauthorized access attempts (although it’s not a foolproof security measure).
- To minimize network clutter in areas with many access points.
- While hidden SSIDs might seem more secure, the real security lies in strong encryption methods like WPA2 with a complex password.
How to Connect to a Hidden SSID:
- Know the SSID: You’ll need to know the exact name of the hidden network you want to connect to. This information might be obtained from the network administrator or someone who already has access.
- Access Wi-Fi Settings: On your device (laptop, smartphone, etc.), navigate to the Wi-Fi settings menu. The exact steps might vary depending on your device and operating system.
- Add a Hidden Network: Look for an option to “Add a new network” or “Manually connect to a network.” This option allows you to enter the SSID and other connection details.
- Provide Security Credentials: Enter the password or other security key required for access to the hidden network. Ensure you have the correct security type selected (WPA2-PSK is recommended for personal networks).
- Connect: Once you’ve entered the SSID, security key, and other relevant settings (like encryption type), attempt to connect to the network.
Important Considerations:
- Security Implications: Hiding the SSID doesn’t provide significant security on its own. It might deter casual attempts, but a determined hacker with proper tools could still discover and potentially exploit the network if it lacks strong encryption.
- Disconnecting and Reconnecting: Depending on your device, you might need to manually re-enter the SSID and password each time you want to connect to a hidden network, unlike readily available networks that can be automatically joined after the initial setup.
Alternatives for Network Security:
- Strong Passwords: Focus on using robust passwords (long, complex combinations of letters, numbers, and symbols) for your Wi-Fi network, regardless of whether the SSID is hidden or visible.
- WPA2 Encryption: Ensure your network uses WPA2 encryption with a strong password for authentication and data protection.
- Guest Network (Optional): If you want to offer limited internet access to guests without exposing your main network, consider setting up a separate guest network with a different SSID and password.
Connecting to a hidden SSID involves knowing the network name and manually entering the details during the connection process. While it might add a small layer of obscurity, remember that strong password practices and encryption are far more critical for robust Wi-Fi security.
802.11 Channel Access Methods: Keeping Order in the Wireless Wild West
Wi-Fi networks operate in a shared wireless medium, meaning multiple devices can potentially transmit data at the same time. This can lead to collisions, where signals from different devices overlap and corrupt each other’s data. To prevent this chaos, 802.11 Wi-Fi utilizes various channel access methods to ensure orderly data transmission.
1. Distributed Coordination Function (DCF):
- Concept: DCF is the fundamental access method defined in the original 802.11 standard. It’s a carrier sense multiple access with collision avoidance (CSMA/CA) approach.
- How it Works:
- Before transmitting, a device listens for any ongoing transmissions on the channel using Carrier Sense.
- If the channel is clear, the device utilizes a mechanism called the Network Allocation Vector (NAV) to estimate the time it will take for any ongoing or upcoming transmissions to finish.
- If the channel is clear and the NAV timer permits, the device transmits a short Request to Send (RTS) frame to the intended receiver.
- If the receiver is available and the channel remains clear, it responds with a Clear to Send (CTS) frame.
- Upon receiving CTS, the device transmits its data packet.
2. Enhanced Distributed Channel Access (EDCA):
- Concept: EDCA is an extension of DCF introduced in later 802.11 standards. It prioritizes traffic based on different categories (voice, video, data) to provide better Quality of Service (QoS) for real-time applications.
- How it Works:
- EDCA builds upon DCF but assigns different access priorities to various data types using Access Categories (ACs).
- ACs like voice or video get higher priority compared to background data traffic, ensuring smoother transmission for time-sensitive applications.
3. Request to Send/Clear to Send (RTS/CTS):
- Concept: RTS/CTS is an optional handshake mechanism within DCF that can further reduce collision risks.
- How it Works:
- As explained in DCF, a device transmits an RTS frame to the receiver before sending data.
- This RTS frame acts as a heads-up for nearby devices, reserving the channel for the upcoming transmission between the sender and receiver.
- The receiver responds with a CTS frame, acknowledging the reservation and allowing the data transmission to proceed.
4. CTS-to-Self:
- Concept: CTS-to-Self is a variation of RTS/CTS used in specific scenarios to improve efficiency.
- How it Works:
- In some situations, a device might be both the sender and receiver (e.g., communicating with an access point in a point-to-point link).
- Instead of sending an RTS frame that requires a response, the device transmits its data directly after a short delay.
- The receiver, which has already received the initial CTS frame from the same device acting as the sender, can start receiving the data without needing another CTS exchange.
5. Network Allocation Vector (NAV):
- Concept: NAV is a crucial element in both DCF and EDCA. It’s a virtual timer that estimates the amount of time the channel will be busy due to ongoing or upcoming transmissions.
- How it Works:
- Devices listen to beacon frames and data packets to determine the transmission duration and update their NAV timers accordingly.
- A device only attempts to transmit when the channel is clear and the NAV timer indicates no impending transmissions, avoiding collisions.
Interframe Spaces
In the world of Wi-Fi (802.11), interframe spaces (IFS) play a vital role in ensuring smooth communication between devices. These IFS act as tiny gaps inserted between frames transmitted over the wireless channel, preventing collisions and maintaining order. Here’s a breakdown of the six main types of IFS:
1. Short Interframe Space (SIFS):
- Function: SIFS is the shortest interframe space used in 802.11 networks. It’s a mandatory gap inserted between frames within the same data exchange sequence.
- Purpose: SIFS guarantees priority to ongoing transmissions. By keeping a minimal gap between frames in a sequence (like data packets and acknowledgements), SIFS ensures other devices hold off from transmitting and interrupting the flow.
- Typical Duration: The duration of SIFS depends on the specific Wi-Fi standard being used. It’s typically around 10 microseconds (µs) for 802.11b/g/n (2.4 GHz) and 16 microseconds (µs) for 802.11a/n/ac (5 GHz).
2. Distributed Coordination Function Interframe Space (DIFS):
- Function: DIFS is used in the Distributed Coordination Function (DCF) access method, a core mechanism for sharing the wireless channel.
- Purpose: DIFS ensures that devices don’t transmit simultaneously, preventing collisions. A device attempting to transmit listens for the channel to be idle for a DIFS duration before initiating its transmission.
- Typical Duration: DIFS is typically longer than SIFS (around 50 microseconds for most 802.11 standards) to account for the time it takes devices to detect a carrier signal and prepare for transmission.
3. Point Coordination Function Interframe Space (PIFS):
- Function: PIFS is used in conjunction with the Point Coordination Function (PCF) access method, which is an optional scheme where a centralized access point controls transmissions.
- Purpose: Similar to SIFS, PIFS provides priority to ongoing transmissions initiated by the access point. Devices using PCF wait for a PIFS duration before attempting their own transmissions.
- Typical Duration: PIFS is typically shorter than DIFS (around 3 microseconds) as the access point coordinates transmissions, reducing the need for extensive listening before attempting access.
4. Extended Interframe Space (EIFS):
- Function: EIFS is the longest interframe space used in 802.11 networks.
- Purpose: EIFS is primarily used after encountering errors or failed transmissions. It provides additional time for devices to recover from potential issues before attempting further transmissions.
- Typical Duration: EIFS is significantly longer than other IFS durations (around a millisecond) to allow ample time for error handling and potential retransmissions.
5. Arbitration Interframe Space (AIFS):
- Function: AIFS is used in conjunction with the EDCA (Enhanced Distributed Channel Access) mechanism, which prioritizes traffic based on different categories (voice, video, data).
- Purpose: AIFS adds an additional delay on top of DIFS for different traffic categories. Higher priority categories (like voice) have shorter AIFS, allowing them to access the channel more quickly.
- Dynamic Nature: Unlike fixed IFS durations like SIFS or DIFS, AIFS can be dynamically adjusted based on the current network load and traffic types.
6. Reduced Interframe Space (RIFS):
- Function: RIFS is a relatively new addition introduced in the 802.11n standard. It’s an even shorter interframe space compared to SIFS.
- Purpose: RIFS is specifically designed for transmissions between devices using the HT (High Throughput) mode in 802.11n. It allows for faster frame bursting and potentially higher data rates.
- Limited Use: RIFS can only be used under specific conditions (like a Greenfield HT network) due to stricter timing requirements. It’s not commonly used in all Wi-Fi scenarios.
Understanding interframe spaces (IFS) is essential for comprehending how Wi-Fi networks manage data flow and avoid collisions. By strategically inserting these gaps between frames, 802.11 standards ensure efficient and orderly communication in the shared wireless environment.
Physical carrier sense and virtual carrier sense
In the realm of Wi-Fi (802.11) networks, both physical carrier sense and virtual carrier sense play crucial roles in preventing collisions and ensuring smooth data transmission. he same explained below::
Physical Carrier Sense (PCS):
- Concept: Physical carrier sense is the most fundamental mechanism. It involves a device literally listening for any existing radio frequency (RF) signals on the channel it intends to use.
- How it Works: Before transmitting any data, a Wi-Fi device actively listens to the chosen channel. This listening process detects the presence of any ongoing transmissions, like signals from other devices already using the channel.
- Think of it as: Imagine you’re trying to have a conversation in a crowded room. Physical carrier sense is like listening to see if anyone else is already talking before you start speaking.
Virtual Carrier Sense (VCS):
- Concept: Virtual carrier sense goes beyond just listening for raw signals. It leverages information within the Wi-Fi protocol to understand channel availability.
- How it Works: There are two main ways VCS is implemented:
- 1. Request to Send/Clear to Send (RTS/CTS): This is an optional handshake mechanism within the DCF (Distributed Coordination Function) access method. A device sends an RTS frame to the intended receiver, indicating its desire to transmit. The receiver responds with a CTS frame if the channel is clear, granting permission to transmit. This exchange provides virtual confirmation of channel availability beyond just physical signal detection.
- 2. Duration/ID field in Beacon frames: In some scenarios, devices can leverage information from beacon frames transmitted by access points (APs). These beacons contain a Duration/ID field that specifies the duration of an ongoing transmission or identifies upcoming transmissions managed by the AP. By decoding this information, a device can gain virtual insight into channel availability before attempting its own transmission.
Think of it as:
- Imagine the crowded room again. In addition to listening for ongoing conversations (physical carrier sense), virtual carrier sense is like:
- Option 1 (RTS/CTS): Briefly raising your hand to get the attention of the person you want to talk to and waiting for their nod before speaking (CTS).
- Option 2 (Beacon frames): Observing a schedule posted on the wall that indicates when the room will be available for presentations or quiet study.
Working Together:
- Physical carrier sense and virtual carrier sense work in tandem to provide a comprehensive understanding of channel availability.
- Physical carrier sense is the first line of defense, ensuring no raw signal collisions occur.
- Virtual carrier sense, through mechanisms like RTS/CTS or beacon frames, adds an extra layer of coordination to avoid conflicts with transmissions managed by other devices or the access point.
Both physical and virtual carrier sense are essential for efficient and collision-free communication in Wi-Fi networks. By combining these methods, devices can share the wireless channel effectively and ensure reliable data transmission.
802.11 MAC Operations
The 802.11 Media Access Control (MAC) layer plays a vital role in managing wireless network connections. A breakdown of key functionalities within this layer are explained below:
1. Roaming:
- Concept: Roaming allows a Wi-Fi device (STA) to seamlessly switch between access points (APs) within the same network while maintaining an active connection. This ensures uninterrupted communication as the device moves around the coverage area.
- How it Works:
- The STA constantly monitors signal strength and quality from nearby APs.
- When a better AP (stronger signal, lower congestion) is detected, the STA initiates a roaming process.
- This process typically involves:
- Sending a disassociation frame to the current AP (optional).
- Authenticating with the new AP using methods like WPA2.
- Re-associating with the new AP to establish a new connection.
- Ideally, roaming happens smoothly and transparently to the user, maintaining ongoing applications and data transfers.
2. Power Save Modes:
- Concept: Wi-Fi devices can consume significant battery power. Power save modes help conserve battery life by allowing the device to enter a sleep state when not actively transmitting or receiving data.
- How it Works:
- There are two main power save modes defined in the 802.11 standard:
- Power Save Mode (PSM): The STA periodically wakes up to check for beacon frames from the AP and any buffered data frames.
- Automatic Power Save Delivery (APSD): This mode is specifically designed for applications with real-time requirements like voice calls or video conferencing. The AP schedules specific times (delivery windows) to transmit data to the STA in power save mode.
- The specific power save mode used depends on the device, network configuration, and application needs.
- There are two main power save modes defined in the 802.11 standard:
3. Frame Buffering:
- Concept: Frame buffering is a mechanism that allows the AP to temporarily store data frames intended for a STA that is currently in power save mode.
- How it Works:
- When a device enters power save mode, it informs the AP of its sleep schedule and wake-up intervals.
- The AP buffers any data frames addressed to the STA during its sleep periods.
- When the STA wakes up according to its power save mode (PSM) or delivery window (APSD), it retrieves the buffered frames from the AP and processes the data.
- Frame buffering ensures that data isn’t lost even when the STA is in a low-power state.
4. Protection Mechanisms:
- Concept: 802.11 networks incorporate various security mechanisms to protect against unauthorized access, data interception, and other malicious activities.
- Common Mechanisms:
- Authentication: Methods like WPA2 with PSK (pre-shared key) ensure only authorized devices can connect to the network.
- Encryption: Data encryption scrambles data during transmission, making it unreadable to eavesdroppers. Standards like WPA2 with AES encryption provide robust protection.
- Access Control: Techniques like MAC filtering can restrict network access to specific devices based on their MAC addresses.
- Integrity Checksums: These checksums verify the integrity of data frames, ensuring they haven’t been tampered with during transmission.
802.11 MAC operations encompass various functionalities like roaming, power saving modes, frame buffering, and protection mechanisms. These features work together to ensure a smooth, reliable, and secure Wi-Fi experience for users. By understanding these operations, you can appreciate the complexities involved in maintaining a stable wireless connection behind the scenes.
WLAN devices, control, and management systems
1. Access Points (APs)
An access point (AP) acts as a wireless hub in a WLAN network, providing connectivity between Wi-Fi devices (stations) and a wired network (like Ethernet). When it comes to managing these APs in Cisco Prime Infrastructure 3.8.1, here’s a breakdown of relevant features, selection considerations, and installation:
Features of Access Points (APs):
- Radio transceivers: Transmit and receive Wi-Fi signals on specific frequencies (2.4 GHz or 5 GHz).
- Network ports: Provide wired connectivity to the network backbone (usually Ethernet).
- Antennas: Radiate and capture Wi-Fi signals. The number and type of antennas can impact coverage area and performance.
- Management capabilities: Allow for configuration, security settings, and monitoring of the AP.
- Power over Ethernet (PoE) support: In some models, PoE supplies power to the AP through the Ethernet cable, simplifying cabling requirements.
Selecting Access Points:
- Network requirements: Determine the size and layout of the area you need to cover, the number of users, and the desired data rates.
- Client device compatibility: Ensure the APs support the Wi-Fi standards (802.11a/b/g/n/ac/ax) used by your devices.
- Security features: Look for APs that support strong encryption standards like WPA2 and WPA3 for secure data transmission.
- Management capabilities: Select APs manageable by Cisco Prime Infrastructure 3.8.1 for centralized control and monitoring.
- Power requirements: PoE simplifies deployment, but some models might require a separate power supply.
Installing Access Points:
The specific installation process can vary depending on the AP model and your network environment. However, here’s a general guideline:
- Choose the locations: Strategically place APs to ensure adequate Wi-Fi coverage throughout the desired area. Consider factors like building materials and potential signal interference.
- Mount the APs: Securely mount the APs on walls or ceilings based on the manufacturer’s instructions.
- Connect the cables: Connect the APs to the network using Ethernet cables. If using PoE, ensure your network switch supports it.
- Power on the APs: Provide power to the APs either through PoE or a separate power supply.
- Configure the APs: Use Cisco Prime Infrastructure 3.8.1 to configure the SSID (network name), security settings, and other parameters for each AP.
By understanding these features, selection criteria, and installation steps, you can effectively deploy and manage access points within your Cisco Prime Infrastructure 3.8.1 environment. Remember to consult the official documentation for specific details and ensure compatibility between your APs and Cisco Prime Infrastructure version.
WLAN Controllers
In the realm of Wireless Local Area Networks (WLANs), WLAN controllers play a central role in managing multiple access points (APs). These controllers act like the brains of a WLAN, simplifying administration, enhancing performance, and providing security features. Here’s a breakdown of WLAN controllers:
What They Do:
- Centralized Management: WLAN controllers offer a unified platform to configure, monitor, and troubleshoot multiple APs from a central location. This eliminates the need to individually configure each AP, saving time and effort for network administrators.
- Scalability: As your network grows, adding more APs becomes easier with a controller. The controller can manage a large number of APs, simplifying administration of extensive WLAN deployments.
- Advanced Features: WLAN controllers often provide advanced functionalities like:
- Policy Enforcement: Enforcing consistent network access policies (security, access control, QoS) across all APs in the network.
- Load Balancing: Distributing network traffic evenly across multiple APs to prevent overloading and ensure optimal performance for connected devices.
- Fast Roaming: Enabling seamless handoff of devices between APs as users move around the coverage area, maintaining uninterrupted connectivity.
- Mesh Networking: In some models, facilitating mesh network configurations where APs can communicate with each other, extending coverage and improving network resilience.
- Security Features: Centralized management of security settings like WPA3 encryption and rogue AP detection for enhanced network protection.
Types of WLAN Controllers:
- Hardware Controllers: These are dedicated physical appliances specifically designed for WLAN controller functionality. They offer robust processing power and scalability for large networks.
- Software Controllers: These are software applications that run on existing hardware, often a server. They can be a cost-effective option for smaller deployments but might have limitations on scalability and processing power compared to dedicated hardware controllers.
Selecting a WLAN Controller:
When choosing a WLAN controller, consider these factors:
- Network Size and Scalability: The number of APs you need to manage and the potential for future growth will influence the required controller capacity.
- Features Required: Identify the features most critical for your network, such as load balancing, fast roaming, or mesh networking.
- Budget: Hardware controllers typically come with a higher upfront cost, while software controllers may require licensing fees. Choose the option that best suits your budget constraints.
- Compatibility: Ensure the controller is compatible with your existing AP models and network infrastructure.
Benefits of Using WLAN Controllers:
- Simplified Management: Centralized control for easier configuration, monitoring, and troubleshooting.
- Improved Performance: Features like load balancing and fast roaming enhance network efficiency and user experience.
- Enhanced Security: Centralized management of security policies strengthens network protection.
- Scalability: Easier to accommodate network growth by adding more APs without significant configuration overhead.
In Conclusion:
WLAN controllers are valuable tools for managing complex wireless networks. By centralizing control, enhancing performance, and offering advanced features, they simplify network administration and ensure a reliable, secure, and efficient Wi-Fi experience for users.
Wireless Network Management Systems
Wireless network management systems (WNMS) are software applications designed to simplify administration, monitor performance, and enhance security of WLAN infrastructures. They act like a command center for your Wi-Fi network, providing a centralized platform to manage numerous access points (APs), improve user experience, and troubleshoot issues.
Core Functions:
- AP Discovery and Inventory: WNMS automatically detect and identify APs within the network, creating a comprehensive inventory for easier management.
- Configuration Management: WNMS allows you to configure settings like SSIDs, security parameters, and access control policies for multiple APs from a central location.
- Performance Monitoring: WNMS provides real-time insights into network performance metrics like signal strength, data throughput, and client connectivity. This helps identify potential bottlenecks and optimize network health.
- Client Management: Some WNM systems offer features to view and manage connected devices, allowing you to set bandwidth limits or restrict access for specific devices.
- Alerting and Reporting: WNMS can generate alerts for critical events like security breaches, AP outages, or performance degradation, enabling proactive troubleshooting. They can also generate reports on network usage, trends, and potential issues.
- Security Management: WNMS helps maintain a strong security posture by allowing centralized management of encryption settings, rogue AP detection, and guest network access.
Benefits of Using WNM Systems:
- Simplified Management: WNMS eliminates the need to configure each AP individually, saving time and effort for network administrators.
- Improved Network Performance: Real-time monitoring and troubleshooting capabilities help identify and address performance issues before they significantly impact users.
- Enhanced Security: Centralized management of security settings strengthens network protection and simplifies detection of potential threats.
- Scalability: WNM systems can manage a large number of APs, making them suitable for growing networks.
- Cost Savings: WNMS can help optimize network performance and prevent downtime, potentially leading to cost savings in the long run.
Types of WNM Systems:
- Cloud-Based WNM Systems: These are web-accessed services that eliminate the need for on-premise hardware. They offer easy deployment and scalability but might have limitations on customization compared to on-premise systems.
- On-Premise WNM Systems: These are software applications installed on a server within your network. They offer more control and customization but require additional hardware and ongoing maintenance.
Choosing a WNM System:
When selecting a WNM system, consider these factors:
- Network Size and Complexity: The number of APs you manage and the features you need will determine the required system’s capabilities.
- Desired Features: Identify the functionalities most important for your network, such as advanced security, detailed reporting, or mesh network support.
- Budget: Cloud-based systems typically have lower upfront costs, while on-premise systems require hardware investment but might offer lower ongoing fees.
- Ease of Use: Consider the user interface and overall manageability of the WNM system.
By providing centralized control, performance insights, and security features, WNM systems streamline network administration and ensure a reliable wireless experience for users.
Wireless Bridge and Mesh APs
Both wireless bridges and mesh AP systems extend the reach of your Wi-Fi network, but they achieve this in different ways and cater to different needs. These are explained in detail in the following paragraphs.
Wireless Bridge:
- Concept: A wireless bridge acts as a dedicated point-to-point connection that extends your existing Wi-Fi network to a wired device. It receives a wireless signal from your main router or access point and then retransmits it as a wired connection (usually Ethernet) to the connected device.
- Typical Use Case: Ideal for situations where you have a device, like a smart TV or gaming console, located far from your router and Ethernet cabling isn’t feasible. The bridge helps connect these devices to your network without running long cables.
- Pros:
- Relatively inexpensive.
- Simple setup process.
- Provides a dedicated, stable connection for the bridged device.
- Cons:
- Only extends the network to one device at a time (requires a separate bridge for each additional device).
- Doesn’t offer the whole-home coverage benefits of mesh systems.
- Limited functionality compared to mesh systems.
Mesh AP System:
- Concept: A mesh AP system consists of multiple wireless access points (nodes) that work together to create a blanket of Wi-Fi coverage throughout your home. These nodes communicate with each other wirelessly, extending the network signal and maintaining a seamless connection as you move around the house.
- Typical Use Case: Perfect for larger homes or buildings where a single router struggles to provide sufficient coverage. Mesh systems are ideal for eliminating dead zones and ensuring consistent Wi-Fi throughout the space.
- Pros:
- Whole-home Wi-Fi coverage.
- Scalable by adding more nodes to expand the network further.
- Often offer features like roaming for uninterrupted connections as you move between nodes.
- May provide additional functionalities like parental controls and guest network options.
- Cons:
- Generally more expensive than wireless bridges.
- Setup process can be slightly more complex than single bridges.
Choosing Between Bridge and Mesh:
Here’s a quick guide to help you decide:
- Need to connect a single device: Go for a wireless bridge if you only have one specific device (like a smart TV) that needs a wired connection due to distance from the router.
- Large home or multiple devices: Opt for a mesh AP system if you have a larger space with coverage issues or want to extend Wi-Fi to multiple devices in different areas.
- Budget: Wireless bridges are a more budget-friendly option, while mesh systems typically have a higher upfront cost.
Additional Considerations:
- Existing Network Setup: Ensure your router or access point is compatible with the chosen bridge or mesh system.
- Technical Expertise: Consider your comfort level with setup processes. Wireless bridges are generally easier to set up, while mesh systems might require a bit more configuration.
By understanding the strengths and weaknesses of wireless bridges and mesh AP systems, you can make an informed decision on the best way to extend your Wi-Fi network and achieve optimal coverage for your needs.
Clients
Client devices, also known as wireless stations (STAs), are the electronic gadgets that connect to a Wi-Fi network to access the internet or communicate with other devices. These devices come in various forms, each with its own capabilities and purposes:
- Laptops and Desktops: These are traditional computing devices that leverage Wi-Fi for internet access, browsing, email, video conferencing, and other online activities.
- Smartphones and Tablets: Mobile devices like smartphones and tablets rely heavily on Wi-Fi for internet connectivity. They use Wi-Fi for web browsing, social media, streaming services, gaming, and downloading applications.
- Smart Home Devices: The growing world of smart home devices, including thermostats, lights, doorbells, and appliances, often connect via Wi-Fi. This allows for remote control, automation, and integration with smart home ecosystems.
- Gaming Consoles: Modern gaming consoles utilize Wi-Fi for online gaming, downloading updates, and accessing online features.
- Printers and Scanners: Some printers and scanners offer Wi-Fi connectivity, enabling wireless printing and scanning from various devices on the network.
- Streaming Devices: Streaming devices like Roku, Chromecast, and Apple TV connect to Wi-Fi to access streaming services, movies, and TV shows on your television.
- Wearables: Smartwatches, fitness trackers, and other wearable devices might utilize Wi-Fi for syncing data with smartphones, downloading updates, and accessing additional features.
These are just a few examples, and the list continues to grow as more and more devices become internet-enabled and Wi-Fi capable. Client devices typically come equipped with a Wi-Fi adapter or built-in Wi-Fi radio that allows them to communicate with access points (APs) in the network.
Key aspects of client devices in a Wi-Fi network given below:
- Wireless Standards: Client devices support different Wi-Fi standards (802.11a/b/g/n/ac/ax) which determine their connection speeds and compatibility with access points.
- Operating Systems: Client devices run various operating systems like Windows, macOS, Android, iOS, and others. These operating systems manage the Wi-Fi connection settings and network interactions.
- Security Protocols: Client devices rely on security protocols like WPA2 and WPA3 to ensure secure communication and data encryption on the Wi-Fi network.
- Power Management: Wi-Fi can drain battery life on mobile devices. Client devices often have power management features to optimize Wi-Fi usage and conserve battery power.
Understanding the role of client devices in a Wi-Fi network is essential for ensuring proper connectivity, performance, and security. By using compatible devices and maintaining proper configurations, users can enjoy a smooth and reliable wireless experience.
References: Tutorialsweb.com https://www.tutorialsweb.com/broadband/index.htm
